Protecting your organization’s data is more important than ever. As businesses become cloud-native, it’s essential to understand how to keep data secure in this environment
Without proper security measures, your sensitive information could be at risk. You may think you’re safe, but how safe are you?
Recent independent research shows that attackers now remain undetected inside victim environments for a median of just 10 days — a sharp drop from the months or even years it once took to identify intrusions. While detection has improved, even a 10-day exposure window can be devastating, giving adversaries ample time to exfiltrate sensitive data, deploy ransomware, or compromise customer trust.
That means the pressure is higher than ever: organizations can no longer rely on luck or slow detection cycles. A strong cloud data security posture is essential to prevent breaches, minimize dwell time, and protect critical assets.
What is cloud data security?
Cloud data security is essential to protecting your organization’s critical systems and data from cyber threats and risks associated with cloud environments. It involves a combination of controls, procedures, and technologies designed to keep your data and systems safe from unauthorized access, misuse, or destruction.
The importance of cloud data security for businesses cannot be overstated. Cloud environments are often more vulnerable to cyber attacks because they are accessed over the internet and shared among multiple users.
The rise of remote working has added an extra layer of complexity to cloud data security. With more employees working from home or other remote locations, it is crucial to ensure that data and systems are protected from unauthorized access, even when accessed outside the office.
Furthermore, the increasing prevalence of security breaches highlights the need for robust cloud data security measures. Organizations must invest in these measures to protect against cyber threats and to comply with growing compliance regulations.
Why is cloud data so challenging to secure?
Securing cloud data can be a frustrating and daunting task. The sheer size and complexity of the cloud make it challenging to protect against potential security threats. Identifying and securing all vulnerabilities is difficult with such a large attack surface and multiple entry points. The lack of visibility into the cloud environment can make it difficult to detect potential security breaches and take appropriate action. These challenges can be overwhelming, leaving organizations feeling helpless and exposed in the face of potential attacks.
Large attack surface
The cloud has a large attack surface, making it particularly vulnerable to attacks. This is because the cloud has multiple points of entry, such as web applications, APIs, and user accounts. This makes it difficult to secure all these entry points and protect against potential attacks.
Complexity
The cloud is complex because it involves multiple components, such as storage, networking, and computing, all of which must be configured and managed. This complexity can make it challenging for organizations to understand and manage their cloud environment, especially if they are not well-versed in cloud technology.
Poor visibility
The cloud has poor visibility because it can be difficult to know what data is stored in it, who has access to it, and how it is used. This lack of visibility can make it challenging to detect potential security breaches and take appropriate action to protect against them.
Shared responsibility confusion
Many breaches stem from misunderstandings about what the cloud provider secures vs. what the customer must secure.
Why do businesses choose to store their data in the cloud?
Businesses often store many data types in the cloud, including sensitive and non-sensitive information. Some common examples of data that companies may store in the cloud include:
1. Customer data
Information such as contact details, purchase history, and other information related to a business’s customers. This type of data can be sensitive, as it may contain personal or financial information that could be used for identity theft or other fraudulent activities if accessed by unauthorized individuals.
2. Financial data
Information such as budgets, revenue projections, and other financial details related to a business. This type of data is often sensitive, as it can contain confidential information that could be used for fraud or other nefarious purposes if accessed by unauthorized individuals.
3. Employee data
Information such as contact details, job titles, and other details related to a business’s employees. This type of data is typically considered sensitive, as it may contain personal information that could be used for identity theft or other fraudulent activities if accessed by unauthorized individuals.
4. Intellectual property
Information such as trade secrets, proprietary technology, and other intellectual property unique to a business. This type of data is often considered highly sensitive, as it could be valuable to competitors or others who may seek to gain access to it without authorization.
In general, sensitive data is any type of information that could be used for fraudulent or malicious purposes if accessed by unauthorized individuals. This can include personal information, financial data, and other types of confidential or proprietary information.
Non-sensitive data, on the other hand, is information that is not confidential or potentially harmful if accessed by unauthorized individuals. Examples of non-sensitive data may include public information, such as a business’s address or phone number, or data that is not considered valuable to potential attackers. Best practices and guides for industrial data security show that operational datasets, while often labeled as non-sensitive, still need protection when hosted in the cloud.

11 Major Cloud Data Security Threats
As businesses increasingly rely on cloud services to store and manage their data, the threat of a security breach looms. Here are 11 major security threats that organizations need to be aware of to protect their sensitive information:
- Malicious insider activity: occurs when an employee with access to an organization’s cloud services intentionally misuses their privileges to steal or damage data.
- Shadow IT: the use of unauthorized cloud services by employees, which can expose an organization to security risks if the services are not correctly configured or secured.
- Compliance violations: If an organization’s cloud services are not properly configured to meet industry regulations and standards, it can lead to significant fines and legal action.
- Misconfiguration of cloud services: If cloud services are not set up properly, they can be vulnerable to attacks and unauthorized access.
- Credential theft: Hackers can steal an organization’s login credentials and use them to gain access to its cloud services, putting sensitive data at risk.
- Unsecured APIs: APIs (Application Programming Interfaces) allow different applications and services to communicate with each other. If they are not properly secured, they can provide a way for hackers to access an organization’s cloud services.
- Access control/unauthorized access: If an organization does not have proper access controls, it can open its cloud services to unauthorized access and manipulation.
- Denial of Service (DoS): occurs when hackers overload a network or server with traffic, rendering it inaccessible to legitimate users.
- Insider threats: In addition to malicious insider activity, employees may also accidentally expose sensitive data due to a lack of training or awareness.
- Reduced infrastructure visibility: As organizations move more of their data and services to the cloud, they may lose visibility and control over their infrastructure, making it more difficult to detect and prevent security threats.
- Data sovereignty/residence/control: As data is stored and managed in different locations worldwide, it becomes more difficult for organizations to ensure that it is protected according to their own laws and regulations. This can lead to issues around data sovereignty, residence, and control.
7 Key Best Practices for Cloud Data Security
When it comes to protecting your data in the cloud, there are several key best practices that you should follow. From knowing your data and understanding the shared responsibility model to encrypt data and controlling user access, these practices can help you ensure the security of your sensitive information.
1. Know Your Cloud Data
When it comes to protecting your organization’s data in the cloud, the first step is to know exactly what data you have and where it’s stored. This is crucial for identifying and safeguarding sensitive information. By conducting regular audits and implementing a data classification system, you can ensure that only necessary data is stored in the cloud and that it’s properly secured. Failing to understand and manage your cloud data properly puts your organization at risk of data breaches and other security incidents.
Don’t let this happen – take control of your cloud data and keep it safe.
Tips:
- Understand what data you have and where it is stored in the cloud
- Conduct regular audits to ensure that only necessary data is stored in the cloud
- Consider implementing a data classification system to help identify sensitive data and apply appropriate security measures
2. Cloud Security as a Shared Responsibility Model
The cloud provider is responsible for securing the infrastructure, while the user is responsible for securing their data and applications. This means that it’s up to you to work with your cloud provider to determine their security measures and what you need to do to secure your data and systems. By understanding and embracing this shared responsibility model, you can ensure that your data is protected and that your organization is prepared for potential security threats.
Don’t leave your data vulnerable – take an active role in securing it in the cloud.
Tips:
- Understand that the cloud provider is responsible for securing the infrastructure, while the user is responsible for securing their data and applications
- Work with your cloud provider to determine what security measures they have in place and what you need to do to ensure the security of your data
- Implement appropriate security measures within your applications and systems
3. Encrypting Data in Transit and at Rest
By encrypting data in transit, such as when it’s transferred over the internet, you can prevent unauthorized parties from accessing it as it moves between systems. Similarly, encrypting data at rest, such as when it’s stored on servers or other storage devices, can protect it from unauthorized access. It’s important to use strong encryption algorithms and regularly update your encryption keys to ensure that your data remains secure.
Don’t take risks with your data – encrypt it to keep it safe.
Tips:
- Encrypt all data in transit, such as when it is being transferred between systems or over the internet
- Encrypt data at rest, such as when it is stored on servers or other storage devices
- Use strong encryption algorithms and regularly update your encryption keys
4. Control User Access
Limiting access to your data and systems is essential for protecting against unauthorized access in the cloud. By implementing strict access controls and authentication methods, such as multi-factor authentication, you can ensure that only authorized users can access your data. Modern practices emphasize automation and codification of access policies throughout the SDLC. A practical guide on Security‑as‑Code building blocks can help teams implement these controls efficiently and consistently.
Don’t let unauthorized individuals gain access to your data – control who has access and keep it safe.
Tips:
- Implement strict access controls to limit who can access your data in the cloud
- Use authentication methods, such as multi-factor authentication, to verify the identity of users before granting access
- Regularly review and update access permissions to ensure that only authorized users have access to sensitive data
5. Upskilling Employees
Your employees are on the front lines of cloud security. Providing training and support can help them protect your organization’s data and systems. By training employees on the importance of cloud security and how to access and use data in the cloud securely, you can empower your employees to take an active role in protecting your organization. Encouraging employees to report any security concerns or potential vulnerabilities can also help identify and address potential threats. Regular security awareness training can ensure that employees are up-to-date on the latest threats and how to protect against them.
Don’t leave your organization’s security in the hands of untrained employees – invest in their knowledge and skills to keep your data safe.
Tips:
- Provide training to your employees on the importance of cloud security and how to securely access and use data in the cloud
- Encourage employees to report any security concerns or potential vulnerabilities
- Implement regular security awareness training to ensure that employees are up-to-date on the latest threats and how to protect against them
6. Respond to Security Incidents
Despite your best efforts, security incidents can still occur. Having a plan in place for responding to these incidents can help you quickly and effectively resolve any issues and minimize the damage. By training employees on how to identify and report potential security incidents, you can ensure that any issues are caught and addressed as quickly as possible. Working with your cloud provider to quickly and effectively resolve any security incidents can also help minimize the impact on your organization.
Don’t be caught off-guard by security incidents – have a plan in place and be prepared to respond.
Tips:
- Have a plan in place for responding to security incidents, such as data breaches or unauthorized access
- Train employees on how to identify and report potential security incidents
- Work with your cloud provider to quickly and effectively resolve any security incidents
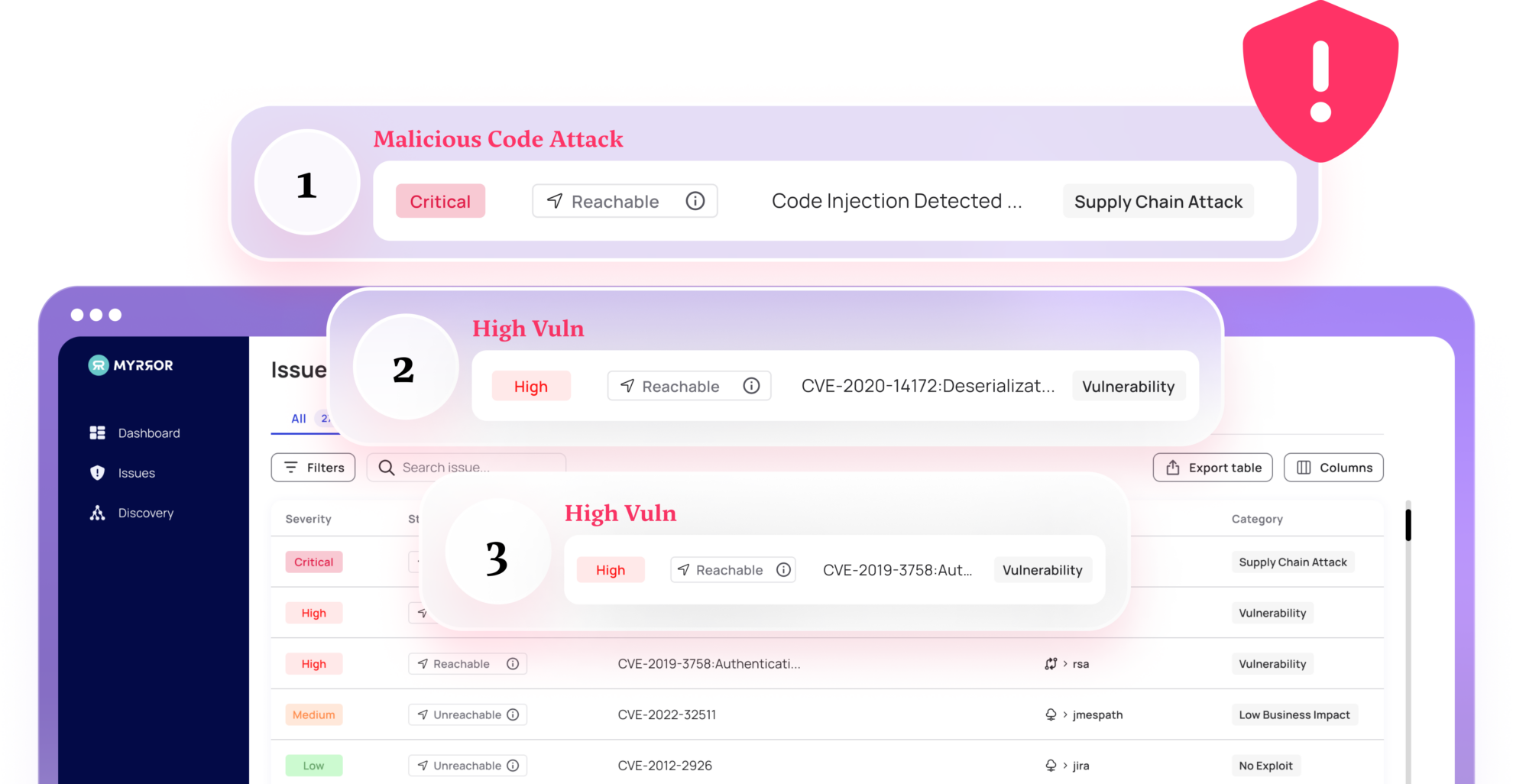
7. Continuously Monitor and Manage Cloud Security
Cloud security is an ongoing process—not a one-time event. Regular monitoring and management are essential for staying ahead of potential threats and ensuring that your data and systems remain secure. An up‑to‑date industry guide on vulnerability management best practices underscores that effective security isn’t just about detection—it’s about embedding accountability, risk‑based triage, and fix validation into the remediation process. You can quickly identify and address potential security vulnerabilities by implementing tools and processes for continuously monitoring your cloud environment. Regularly reviewing and updating your security policies and procedures can also help ensure that they remain effective and up-to-date. Working with your cloud provider to identify and address potential security vulnerabilities can also help protect your organization.
Don’t let your guard down – continuously monitor and manage your cloud security to keep your data safe.
Tips:
- Implement tools and processes for continuously monitoring your cloud environment for potential security threats
- Regularly review and update your security policies and procedures to ensure that they are effective and up-to-date
- Work with your cloud provider to identify and address any potential security vulnerabilities in a timely manner
Keep your cloud data secure
When it comes to protecting your organization’s data in the cloud, it’s crucial to follow best practices. From knowing your data and embracing the shared responsibility model to encrypting data and controlling user access, these practices can help you reduce the risk of security incidents and keep your sensitive information safe. However, implementing these best practices can be challenging, especially for organizations with large amounts of data and complex cloud environments.